Marketing Strategies
4 Proven Business Survival Strategies for Home Improvement Companies
We, like you, are struggling with the shutdown. In addition to having to close physical offices, many of our clients are experiencing significant cancellations of orders. The key is how to keep the business that you have and provide options to customers to keep them from canceling. If you are dealing with cancellations of projects, a drying up of your pipeline, and wondering where your next sale will come from, you are not alone. The steps you take next could determine survival during a prolonged recession or market downturn that we’ve not seen since 2008.
Here are 4 proven options that we’ve deployed with our clients that we want to share with you.
Email Marketing
Consider using professional email address
As an agency, we work with hundreds of clients and we see email addresses like [email protected]. I find this troubling for many reasons. There was a time where it seemed to be ok for a small business to have a non-company email address. But in today’s world – getting emails from companies with a yahoo, Gmail, Hotmail or AOL (yikes) address is sending a really bad message.
So what message are you sending? Read More
Web Design
The Importance of Engagement
Every time we build a website we focus on 3 major elements.
- Web Traffic – growing visitors to your website
- Engagement – how long they stay on your site
- Conversions – what the customer does – eg. calls, appointment requests, quote request
Focus on Engagement. In this post, we are focusing on engagement. We define “engagement” as how relevant and interesting the site is keeping the prospective buyer’s attention. The general idea is that the more engaged your potential customers are, the more time they spend on your site. The longer they stay, the more likely they will call, schedule an appointment or show up at your showroom or retail store and become a customer.
The Top 3 Most Engaging Items. Over the past 5 years we have learned through extensive study and analytics that customers shopping for kitchen and bath products and services like countertops, cabinets and tile, look for 3 major things… Read More
Uncategorized
LinkedIn for Growing Commercial Business
You probably think that LinkedIn won’t help you grow your countertop, cabinet or tile business. For most people, this is absolutely true. For a few smart business owners or sales managers that are open to trying new things our LinkedIn program really works.
Commercial vs. Residential Business. For many of our clients, their focus is on growing residential customers (B2C). Some of our clients only focus on commercial work (B2B). In either case – all of our clients seek repeat business from interior designers, builders, contractors, property management companies, architects, construction company and more.
How Does Networking Work? LinkedIn is the world’s largest networking site. People that are on it expect to connect with others that are in similar businesses. Potential customers, vendors, and employees or employers are expecting to communicate with each other. That means if you are a countertop fabricator, or cabinet company – custom home builders, kitchen remodelers, and contracts may want to “connect” with you and vice versa. Read More
Uncategorized
Learn to be a LinkedIn All-Star
 Did you know that Linkedin ranks you? There are different levels of users and your ranking is based on several criteria. Your goal is to become an All-Star. Your rank is actually a profile strength meter. Your profile strength meter is on the right side of your profile and gauges how robust your profile is. Your strength will increase as you add more content. Here are a few tips to becoming an All-Star. Read More
Did you know that Linkedin ranks you? There are different levels of users and your ranking is based on several criteria. Your goal is to become an All-Star. Your rank is actually a profile strength meter. Your profile strength meter is on the right side of your profile and gauges how robust your profile is. Your strength will increase as you add more content. Here are a few tips to becoming an All-Star. Read More
Website Security
IDNS Scam – please trash these letters
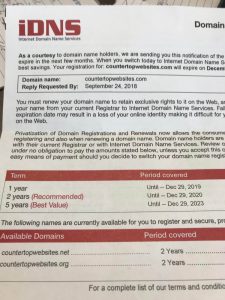
IDNS is a scam.
Today I received this in the mail. It reminded me that several of our clients contacted me that they got this same letter. Let me very clear. This company is a scam. IDNS (Internet Domain Name Service) is not a legitimate service provider. Through this letter away and never waste your time contacting them or worrying about it. While they may be a real company – they are nothing but a fraud. They either purchase names and addresses from the domain name hosting companies or do something known as “scraping” domain owner contact information from the internet. Read More
Website Security
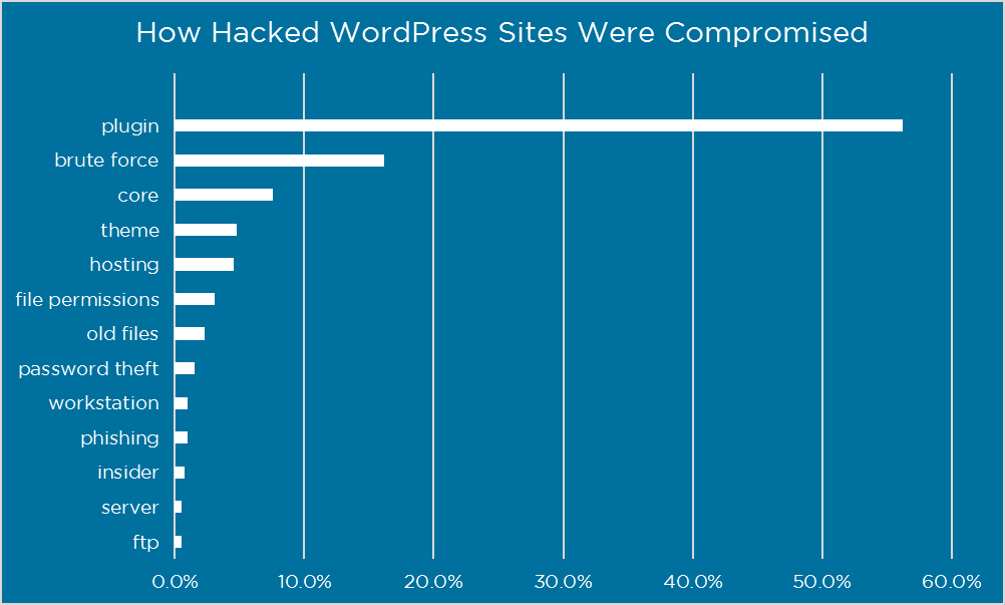
Does your worpress site need security plugins
This is reprinted post from Wordfence, a vendor that we use on all of our sites. Search Traffic Now requires security plugins because of the nature of wordpress, being open source, and the fact that both humans and bots are trying to hack wordpress site approximately every 5 minutes. Moreover, when we host and manage your site, we do not stop with security plugins, our servers all have special software designed to restrict malicious traffic, software to prevent server and website side intrusion and we also use 3rd party platforms like Cloudflare that offer another layer of security between the server, browser, and website. This is an interesting article – please enjoy.
Do You Need a WordPress Security Plugin?
This entry was posted in General Security, Wordfence, WordPress Security on January 25, 2017 by Mark Maunder.
Website Security
What Website Owners Should Know About Security
This blog is about WordPress security. While WordPress is the world’s most popular software for websites – as open source software it’s prone to hacks and attacks. Sadly, we, as web hosting and development companies spend far too much time worrying and working on being vigilant on behalf of our clients who rely on us. For clie Read More
Uncategorized
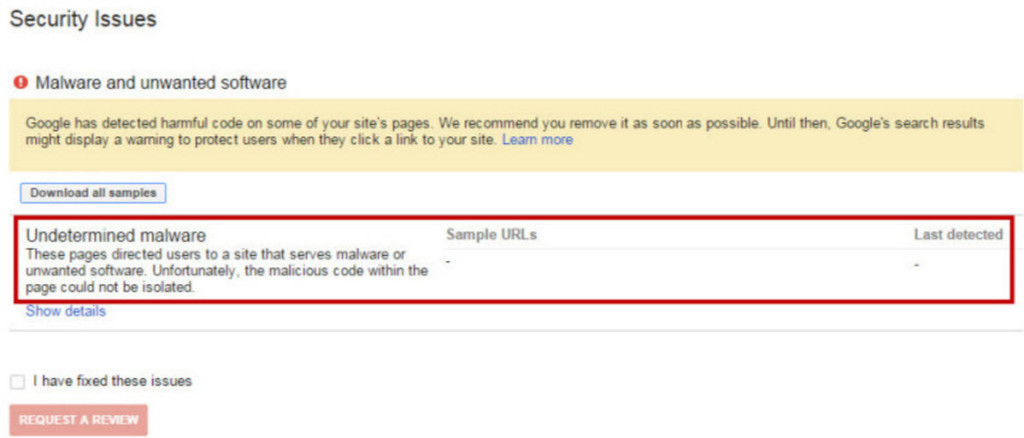
Does a Hacked Website affect Organic Search & SEO
How does a hacked website impact SEO
Websites can be hacked in many ways – most customers don’t even know they’ve been hacked until someone or some service tells them. Google has gotten better a not only finding hacke Read More
Email Marketing
4 Great Reasons to Use HTML Emails for marketing
Email marketing messages come in two different forms — HTML email and plain text email. What’s the d Read More